Local Administrator Password Solution (LAPS) is a new tool that gives the power to manage local Administrator accounts passwords (RID-500).
The most important benefit of deploying LAPS is to mitigate Pass-the-Hash (PtH) credential attack.
By configuring LAPS, Local Administrator on each machine will have its own (unique) complex password. This password changes randomly as per LAPS configuration has been set before and will not be known by anyone except those users who grant the needed permissions to view this password like helpdesk users.
i.e. LAPS applies on Windows Vista SP2, Windows Server 2003 SP2 and later.
Let’s start to deploying LAPS by following the below steps:
1. Preparing for LAPS:
- Download LAPS from Microsoft official site by following the link
- Create the following groups:
- LAPS Exception Servers – LAPS policy will not be applied on group members.
- View Servers Admin Password – group members have the right to view local administrator password of servers.
- View Client Admin Password – group members have the right to view local administrator password of workstations.
- Reset Server Admin Password – group members have the right to reset local administrator password of servers.
- Reset Client Admin Password – group members have the right to reset local administrator password of workstations.
- Store “LAPS.x64.msi”, “LAPS.x86.msi” files in shared folder and make sure that it is accessible from all domain machines.
2. Install LAPS on Management Machine:
- Locate LAPS file you just downloaded and run it.

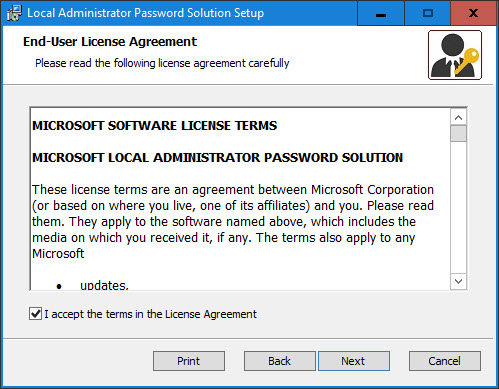

Click Next.
Accept the license and then click Next.
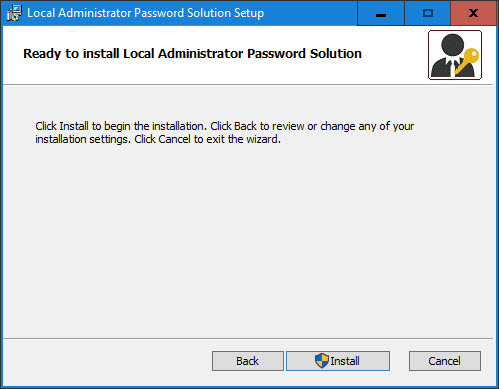
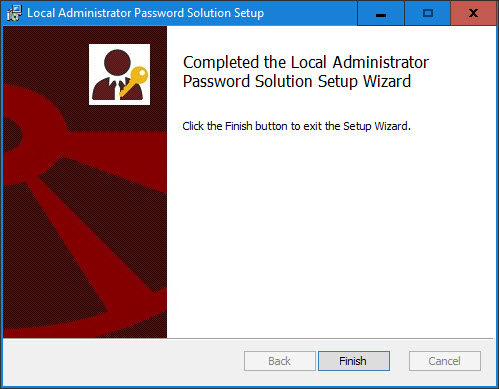
Choose all components and click Next.
Click Install (accept UAC if appeared).
Click Finish.
3. Creating Group Policy Object to install LAPS on domain machines:
- Create new GPO and add both x86, x64 LAPS packages:



go to Computer Configuration–> Policies–> Software Settings–> Software installation–> right click–> new–> Package…
Add both x64 and x86 packages as shown above from shared folder that created in preparation procedure.
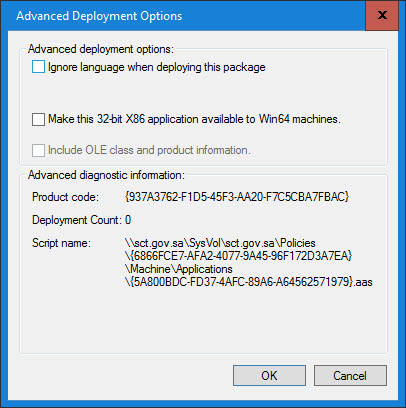
To configure x86 to install only on 32-bit machines:
Choose LAPS x86 package –> right click–> properties–> open Deployment tab then click Advanced button.
Remove “Make this 32-bit X86 application available to Win64 machines” check.
- Link GPO you just created to the needed OU or to the root domain.

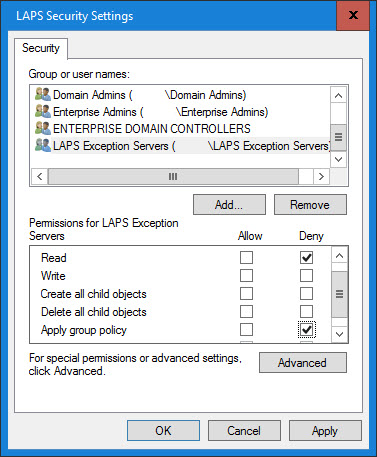

Note: you can exclude specific computers (like: Domain Controllers) from LAPS GPO by choosing GPO and doing the following:
Go to Delegation tab.
To exclude specific servers from installing LAPS on them, add “LAPS Exception Servers” group that created in preparation section above –> and deny Read, Apply group policy permissions.
i.e. GPO will apply by installing LAPS once client machine boot up.
i.e. To verify that LAPS installed successfully on client machine, open Program and Features:
3. Extending AD Schema:
- Run the below commands:
Import-Module AdmPwd.PS Update-AdmPwsADSchema
i.e. above command must be run on schema maser role domain controller by user who is located in “Schema Admins” group.
Note: After extending schema, the below attributes will be added:
ms-MCS-AdmPwd – “stores the password itself”.
ms-MCS-AdmPwdExpirationTime – “stores password expiration”.
4. Removing Extended Rights:

By default all users have the right to read any Active Directory object’s properties including ‘ms-MCS-AdmPwd’ attribute which has local administrator password.
So you have to deny users from read “All extended rights” on the needed OUs as below:
Open Active Directory Users and Computers –> View –> Advanced Features–> Choose the needed OU that contains domain machines (Usually its Computer container) –> right click–> Security tab–> Advanced –> choose the user who has the permission–> Edit, then Remove “All extended rights” check –> Ok –> Apply –> Ok.
Note: To view who has “Extended Right” permission on a specific OU run the command:
Import-Module AdmPwd.PS Find-AdmPwdExtendedrights -identity <OUName> | Format-Table ExtendedRightHolders
5. Adding machine rights:
- To make computers able to change their local administrator passwords. Thus, write permission must be granted to SELF built-in account on both ms-Mcs-AdmPwd, ms-Mcs-AdmPwdExpirationTime attributes. So computer will have the permission to change its local administrator password only. This can be done by running the command:
Set-AdmPwdComputerSelfPermission -OrgUnit <OUName>
Note: This command must be run on all OUs that contain computer accounts you want to apply LAPS on.
Note: You can grant all computers the right to change their administrator passwords on all OUs in the organization by running the command:
Get-ADOrganizationalUnit -Filter * | Set-AdmPwdComputerSelfPermission
6. Adding User rights:
- In this step we will grant users (e.g. helpdesk users) the right to view local administrator password of LAPS applied policy.
Run the below command to grant “View Servers Admin Password” members read local admin password right of server computers:
Set-AdmPwdReadPasswordPermission -OrgUnit <OUName> -AllowedPrincipals "View Servers Admin Password"
Run the below command to grant “View Client Admin Password” members read local admin password right of client computers:
Set-AdmPwdReadPasswordPermission -OrgUnit <OUName> -AllowedPrincipals "View Client Admin Password"
Grant specific users reset password permission so they can change local admin password for both Servers and Client machines, by running the commands:
Set-AdmPwdResetPasswordPermission -OrgUnit <OUName> -AllowedPrincipals "Reset Server Admin Password" Set-AdmPwdResetPasswordPermission -OrgUnit <OUName> -AllowedPrincipals "Reset Client Admin Password"
Additionally, we need to enable auditing for all users in case of read or reset local admin password, by running the command:
Set-AdmPwdAuditing -OrgUnit <OUName> -AuditedPrincipals "Authenticated Users"
Note: when password successfully read, 4662 event id will be logged on DC security logs.
7. Configuring LAPS Group Policy:
Let’s configure LAPS settings by using Group Policy by following the below steps:
- Open LAPS GPO and locate the path Computer Configuration–> Administrative Templates–> LAPS.

- Enable Enable local admin password management setting:

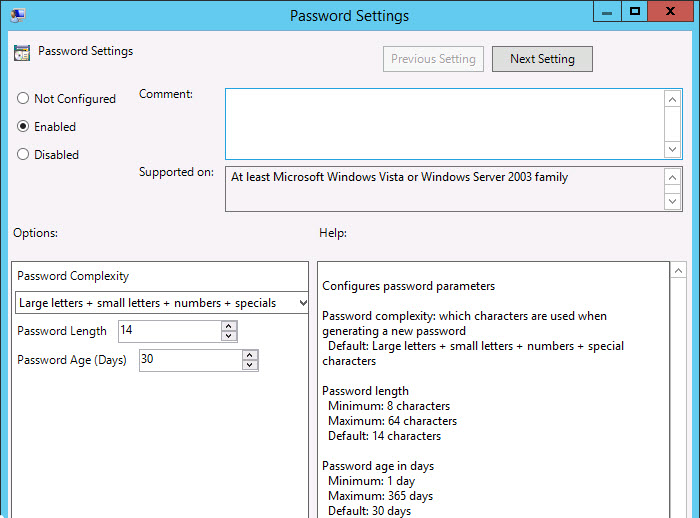
- Configure Password Settings as below:
- Password Complexity: Large letter + small letters + numbers + specials
- Password Length: 14
- Password Age (Days): 30
- Enable Do not allow password expiration time longer than required by policy:

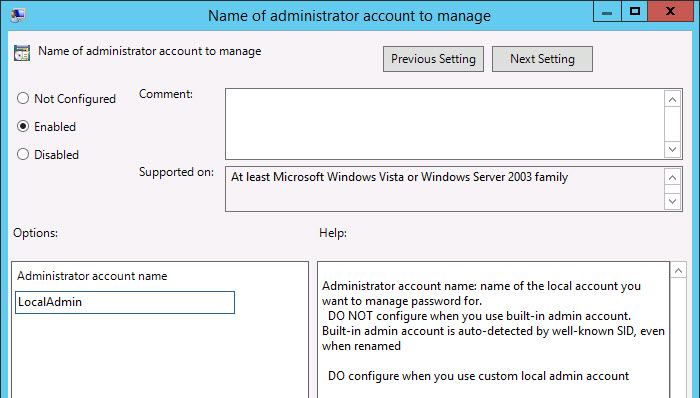
- Additional setting, if you are change the local administrator name to another name different than the default one which is Administrator. Type the local admin name you are configuring on domain machines in Name of administrator account to manage setting:
4. Additional step, Rename Local Administrator by using Group Policy:
I prefer to change the default local administrator name from security perspective, by following the below steps:
- Create new GPO and edit it by following the path Computer Configuration–> Policies–> Windows Settings–> Security Settings–> Local Policies–> Security Options–> open the settings Accounts: Rename administrator account.

- Type the new local administrator name you need (e.g. LocalAdmin):

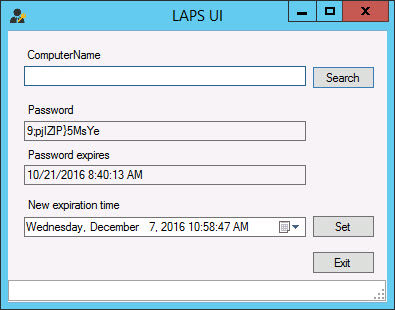
8. Viewing local admin password:.
To view Local Admin password you have the below three options:
- From Active Directory Users and Computers, locate computer account, then view ms-Mcs-AdmPwd attribute:

- From LAPS UI Tool, type the computer name then search button:
- By running one of the below power shell commands:
Get-AdmPwdPassword -ComputerName <ComputerName> Get-ADComputer <ComputerName> -Properties ms-Mcs-AdmPwd | select name, ms-Mcs-AdmPwd
Note: To reset local admin password on specific machine, run the below power shell command:
Reset-AdmPwdPassword -ComputerName <ComputerName> -WhenEffective <DateTime> Ref: https://azureera.com/local-administrator-password-solution-laps/#:~:text=Local%20Administrator%20Password%20Solution%20(LAPS)%201%201.%20Preparing,...%207%207.%20Configuring%20LAPS%20Group%20Policy%3A